Misspelled websites leave you open to hacking and cyberattacks.
This emerging threat is one of many #ShadyHacks affecting millions every day. Using misspelled URLs of well-known brands (aka typosquatting) is a type of brandjacking, where malicious hackers use trusted brands to lure in and exploit businesses and their employees.
Our ethical hackers bring the expertise—and the spice—to protect your business from brandjacking and more, and you can check out Huntress security awareness training episodes for free to see how we do it.

What is brandjacking?
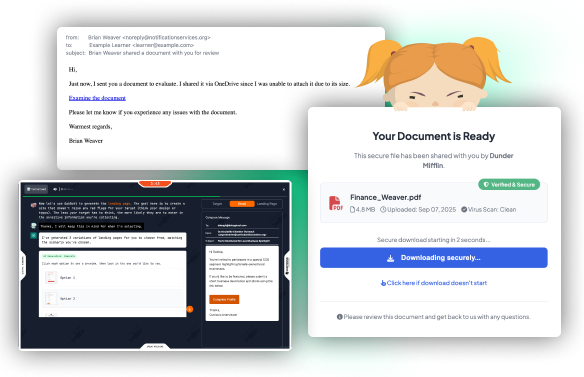
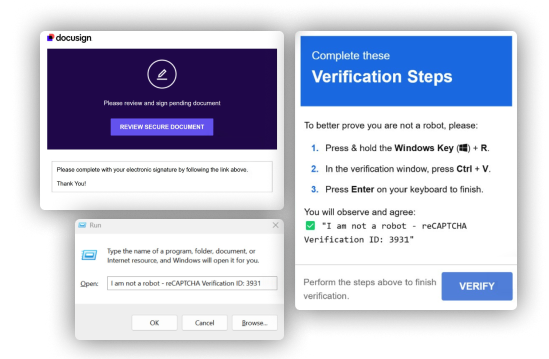
Brandjacking is where hackers impersonate a known brand or company to commit fraud using misspelled URLs, fake emails and text messages, bogus job postings, and/or stolen credentials. This can also lead to bigger, more malicious attacks like ransomware that can affect your business, using gaps or weak links to get into your environment and steal your data.
Malicious hackers also use generative AI for brandjacking attacks like:

Falsifying information through video or photo, typically used for malicious purposes.

A deepfake that creates an exact replica of a trusted person’s voice, used to lure victims into sending valuable data.

Emails or text messages that look like they’re from your CEO or HR team, targeting people with convincing attacks.
All it takes is one employee to fall for these attacks, and BOOM—now hackers have their Microsoft 365 credentials, paving the way for more hacks. But Huntress helps protect you, your employees, and your business from #ShadyHacks and more.

Empower Your People to Spot Brandjacking
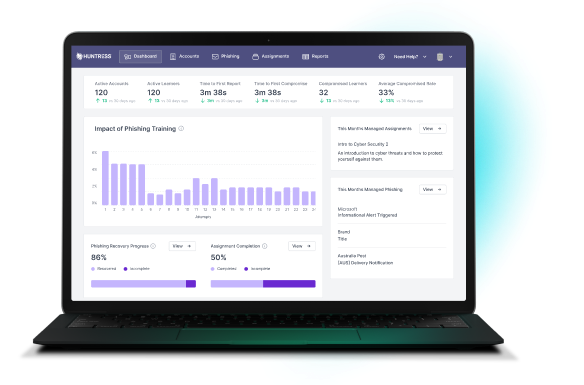
Huntress Managed Security Awareness Training (SAT) gets your employees into the mind of a hacker so they can understand, spot, and stop modern cyberthreats before they wreck your business.
Check out these free episodes to help you and your team make human risk management easier!
Other #ShadyHacks You Need to Watch Out For

SHADY HACK
Ransomware
HOW YOU STOP IT
Endpoint Detection and Response

SHADY HACK
Business Email Compromise

HOW YOU STOP IT
Identity Threat Detection and Response
SHADY HACK
Digital Account Theft
HOW YOU STOP IT
Security Information and Event Management
SIEM, or Security Information and Event Management, collects and analyzes data from across your network to spot and manage threats. It works with EDR and ITDR solutions, correlating data to give you lightning-fast alerts on potential endpoint and identity threats. Huntress Managed SIEM gives your business quick, relevant alerts to stay safe and compliant.

SHADY HACK
Phishing
HOW YOU STOP IT
Security Awareness Training (SAT)
SAT, or Security Awareness Training, teaches employees how to spot and stop potential threats in your digital environment. Huntress Managed SAT is just-in-time training designed by experts in human risk management to get your users to think like hackers, so they can spot digital schemes and neutralize them before they wreck your business.
Join us today in the fight against #ShadyHacks.
Have a story about brandjacking? Share it along with any of the #ShadyHacks on social and join the conversation.
Want to know how your business can get involved?




