When it comes to defending against cyber threats, what if we told you some of the most valuable tools in your arsenal are... completely free? Yes, we’re talking about Open-Source Intelligence (OSINT).
If you’re in cybersecurity and haven’t added OSINT to your playbook, you’re missing out on a powerful way to uncover vulnerabilities, assess threats, and gather critical insights. But what exactly is OSINT, how does it work, and why is it so important? Stick with us—we’re breaking it all down for you in this guide.
What is OSINT?
Open-Source Intelligence (OSINT) is a fancy way of saying "collecting and analyzing publicly available data to gain actionable insights." This information could come from websites, social media, government records, news articles, blogs, or even leaked data on the dark web. The key? It’s all legally and openly accessible.
But here’s the real trick of OSINT—that mountain of raw data isn’t useful until you analyze and interpret it to form complete, actionable intelligence. Think of OSINT as turning “I saw this on Twitter” into “This user’s activity aligns with well-known adversary tactics.”
OSINT vs. just Googling stuff
Sure, anyone can Google, scroll through Reddit, or do a WHOIS lookup. But simply gathering raw information doesn’t make you an OSINT pro. What sets OSINT apart is context.
For example:
-
Raw data = A user posted “I can’t wait for my new job with XCorp!” in a public forum.
-
OSINT analysis = The user has unknowingly leaked an upcoming acquisition by XCorp, giving adversaries a window to exploit insider information.
OSINT isn’t just about what you find; it’s how you interpret it.
Why OSINT matters in cybersecurity
Cybercriminals are watching your public-facing data like hawks. That 4-year-old PDF on your site that contains outdated employee email addresses? Jackpot for a phishing campaign. Misconfigured cloud storage visible through Shodan? A hacker’s dream.
Here’s the harsh truth: If bad actors are using OSINT, shouldn’t you be, too?
Some solid use cases for cybersecurity professionals include:
-
Penetration Testing: Use OSINT tools to scout vulnerabilities before red team exercises.
-
Threat Actor Profiling: Learn the habits, tools, and social connections of threat actors.
-
Monitoring Data Leakage: Catch sensitive company or employee details that are publicly exposed online.
- Social Engineering Defense: Assess how much information about your team is easily accessible for phishing or impersonation scams.

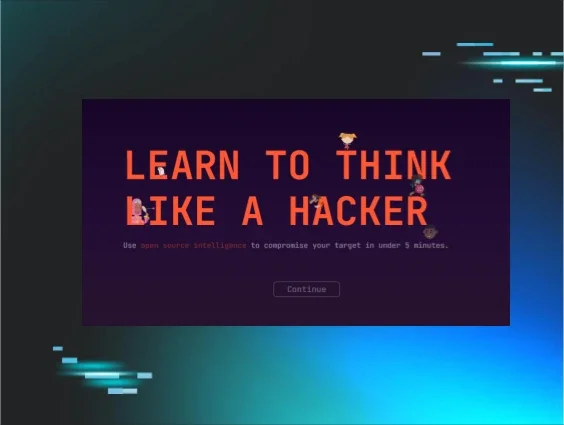
Huntress Managed SAT
A Whole New Way to Train: Introducing Threat Simulator
We’re introducing the brand new Threat Simulator from Huntress Managed SAT. Now, you can more effectively shift learners’ behaviors by reinforcing training with a hands-on, immersive experience that goes beyond just phishing simulations.
Building OSINT into your cybersecurity strategy
Successfully using OSINT requires more than hitting “search.” It involves following a defined process known as the Intelligence Cycle:
-
Preparation: Clearly define your objectives. Are you mapping attack vectors? Monitoring brand mentions in forums?
-
Collection: Gather data from targeted open sources like websites, social platforms, and public records.
-
Processing: Filter out irrelevant findings. Beware of drowning in a sea of useless data.
-
Analysis: Correlate findings to identify patterns and risks.
-
Dissemination: Share actionable intelligence through structured reports, dashboards, or alerts.
Pro tip⚡Input from your OSINT findings isn’t a one-and-done deal. Think of it as a living part of your security arsenal, requiring updates and refinements over time.
The ethical and risky sides of OSINT
One of OSINT’s biggest advantages is also one of its key challenges. The same public data you can use to protect your organization can also be exploited by attackers.
How cybercriminals use OSINT
Bad actors weaponize public information to:
-
Build fake social media profiles for phishing.
-
Conduct Google dorking to locate unprotected files or endpoints.
-
Identify unpatched systems, open ports, or leaked login credentials.
This is why proactive OSINT is so important. If you don’t regularly monitor what’s publicly visible about your organization, you’re at risk of being blindsided by attackers.
Stay ethical, stay legal
While OSINT deals strictly with public info, that doesn’t mean it’s a free-for-all. You should always remain compliant with laws (like GDPR or the CCPA) and ethical guidelines. Steer clear of tactics like hacking, impersonating, or joining private groups under false pretenses. Dodgy tactics can land you in hot water, even with “public” data.
Transparency is key. Document every step of your OSINT process to create a clear audit trail.
Tools of the trade: Best OSINT tools for cybersecurity
You don’t need to reinvent the wheel when it comes to OSINT. Here are some go-to tools used by professionals:
-
Maltego: Create visual link maps between people, domains, networks, and more.
-
Shodan: Find IoT devices and exposed systems on the web.
-
TheHarvester: Gather info on domains, subdomains, and corporate emails.
-
SpiderFoot: Automate OSINT tasks and dig deep into data sets.
-
Google Dorking: Advanced Google searches (like filetype:xlsx site:[companyname]) to uncover hidden files.
-
Recon-ng; A modular framework for multi-source web reconnaissance.
- OSINT Framework: A directory of categorized tools for tasks like finding usernames, email lookups, and more.
Explore the Huntress Managed SAT Episode

Open Source Intelligence (OSINT)
Learn how hackers can use public sources to gather personal or sensitive details about people or organizations in this Managed Security Awareness Training episode.
Real-World OSINT applications in action
Need a few examples of how OSINT works in practice? Consider these scenarios:
-
Penetration Testing: Before launching an internal attack simulation, test your own attack surface by gathering OSINT intel.
-
Incident Response: Did a breach occur? Use OSINT to trace the leaked data and assess its reach. (Dark web monitoring, anyone?)
-
Digital Footprint Mapping: Regularly assess your organization’s visible data, from public Twitter posts to forgotten GitHub repos.
See how these small steps add up to a stronger security posture?
OSINT isn’t perfect (but it’s pretty good)
While OSINT is one of the most powerful tools in a cybersecurity pro's arsenal, it does come with challenges:
-
Information Overload: It’s easy to get buried in meaningless data. Use AI and automation tools to reduce noise.
-
Misinformation: Public data isn’t always accurate. Vet your sources to avoid running down the wrong rabbit holes.
- Time-Intensive: Parsing useful info from raw data can take hours. Having a well-defined OSINT workflow is a lifesaver.
Why you should start using OSINT today
Cyber threats are becoming more sophisticated every second, so it’s crucial to get ahead of the curve. By adopting OSINT strategies, you’ll proactively reduce risks, identify vulnerabilities, and make your organization a tougher target for attackers.
Stay one step ahead of the bad guys. Start integrating OSINT into your cybersecurity workflow today.

Related Resources


Provide an Impactful SAT Experience
Don’t just check a compliance box. Elevate your workplace’s security culture while giving your employees an enjoyable experience.