Have you noticed that nearly every website you visit pops up with a notification asking if you accept cookies? But what exactly are internet cookies, and what do they do? Are they safe to accept? Or are they snooping on your online activity?
We’re breaking it all down in this guide to help you better understand cookies, how they work, and the different types you might encounter while browsing.
What are cookies?
Cookies, in the digital sense and not the delicious Oreo’s sense, are small text files created by websites and stored on your browser. Think of them as ID cards that websites use to recognize you and track certain aspects of your activity. These files allow websites to remember things like your login information, language preference, or what items you’ve added to your shopping cart.
Without cookies, every time you visit a website, you’d essentially be a stranger starting from scratch.
What do cookies do?
Cookies serve various purposes, many of which are designed to improve users' browsing experience. Here’s what they can do:
Remember your preferences: Ever noticed how an e-commerce site remembers your preferred currency or display settings? You can thank cookies for that.
Keep you logged in: Whether it’s your email account or your favorite social media platform, cookies save you the hassle of logging in every single time.
Help websites gather analytics: Website owners use cookies to understand how users interact with their site. For example, cookies can tell them which pages are popular or how long users stay on the website.
Tailor ads to you: Ever wondered why an online store you visited just once starts showing you ads everywhere? Cookies allow advertisers to target you with relevant ads based on your browsing habits.
While cookies can make your online life more convenient, they’re not without risks, which leads us to our next point.
Are Internet cookies safe?
Not all cookies are created equally, and while many are harmless, some can be used for invasive tracking or even malicious purposes. Here’s what you need to know about their safety:
-
First-party cookies (safe in most cases): These come directly from the website you’re visiting. They’re typically used to enhance the website’s functionality, like keeping you logged in or remembering your preferences.
-
Third-party cookies (more concerning): These are created by a domain other than the site you’re visiting. They’re often used by advertisers to track your behavior across multiple websites—as such, they tend to raise privacy concerns.
- Malicious cookies (rare): Although rare, harmful cookies can be used by cybercriminals to track your activity or steal personal information. This is why it’s essential to keep your browser and security settings up to date.
So, should you accept all cookies?
If a website asks for consent to cookies, it’s usually a good sign that they’re adhering to legal standards like GDPR or CCPA, which aim to protect your data privacy. Here’s what we recommend:
Accept cookies from trusted sites to enjoy their full functionality (e.g., your bank or favorite e-commerce platform).
Be cautious with third-party cookies, especially on unfamiliar or suspicious websites.
Always review a site’s cookie policy if you’re unsure what data they’re collecting.
How do Cookies compare to caches and local storage?
Cookies are often confused with other browser storage methods like cache and local storage, but they serve different purposes.
Cookies: Small text files used to store user-specific information like session IDs, preferences, and tracking data. They are sent back to the server with every request, which can impact performance.
Cache: Stores larger files like images, CSS, and JavaScript files to speed up website loading times. The goal is performance, not storing user data. When you revisit a site, your browser can load these files from the cache instead of re-downloading them.
Local Storage: A more modern and robust storage method. It can hold much more data than cookies (around 5-10 MB), and the data isn't sent to the server with every request. It's often used for storing application states or user data for offline use.
Think of it this way: cookies are like a name tag, the cache is like a photo album of the site, and local storage is like a personal notebook for the website to use on your device.
Types of cookies you should know about
Cookies come in various types, and understanding them will help you make informed decisions when browsing online.
1. Session Cookies
These are temporary cookies that are deleted as soon as you close your browser.
They’re often used to track your progress on a website during a single visit (like navigating an online shopping cart).
2. Persistent Cookies
These remain on your device even after you close your browser, lasting until they expire or you manually delete them.
Commonly used to save preferences or keep you logged into your accounts.
3. First-Party Cookies
Set directly by the website you’re visiting.
Typically considered safe and used to improve your on-site experience.
4. Third-Party Cookies
Set by external domains (e.g., advertisers).
Used for tracking across different websites, often raising privacy concerns.
5. Secure Cookies
Only transmitted over encrypted connections (HTTPS).
These help protect sensitive information, like login credentials.
How to clear your cookies
Want to wipe the slate clean? Regularly clearing your cookies can enhance your privacy and even resolve some browsing issues. Here’s how to do it on popular browsers:
Google Chrome:
Go to Settings > Privacy and security > Clear browsing data.
Select "Cookies and other site data."
Choose your time range and click "Clear data."
Mozilla Firefox:
Go to Settings > Privacy & Security.
Scroll down to "Cookies and Site Data" and click "Clear Data."
Check "Cookies and Site Data" and click "Clear."
Microsoft Edge:
Go to Settings > Privacy, search, and services.
Under "Clear browsing data," click "Choose what to clear."
Select "Cookies and other site data" and click "Clear now."
Safari:
Go to Safari > Settings > Privacy.
Click "Manage Website Data."
Select one or more websites, then click "Remove" or "Remove All."
Take control of your cookies
Want to ensure your browsing experience stays both convenient and secure? Here are some proactive steps you can take to manage cookies effectively:
Adjust your browser settings
Use private browsing
Clear your cookies regularly
Install privacy-focused tools
Tools like ad blockers or privacy extensions can help block third-party trackers and safeguard your browsing.
Cookies play a crucial role in enhancing your online experience, from keeping you logged in to personalizing your favorite websites. However, they also come with privacy concerns, especially when it comes to third-party tracking.
By understanding what cookies are, the different types, and how to manage them, you can enjoy the benefits they provide while minimizing potential risks.
Stay informed, stay vigilant, and remember that you have control over your online privacy.
FAQ about Cookies
Yes, some do. Third-party cookies are specifically designed to track your browsing activity across different websites to build a profile of your interests for targeted advertising. First-party cookies also track activity, but only on the site you're currently visiting.
First-party cookies are set by the website you are directly visiting. They are generally used for basic functionality. Third-party cookies are set by other domains, like advertisers or analytics services embedded on the site you're visiting. They are the primary tool for cross-site tracking.
Regulations like the GDPR in Europe and the CCPA in California require websites to get your consent before storing non-essential cookies on your device. This transparency gives you control over your data.
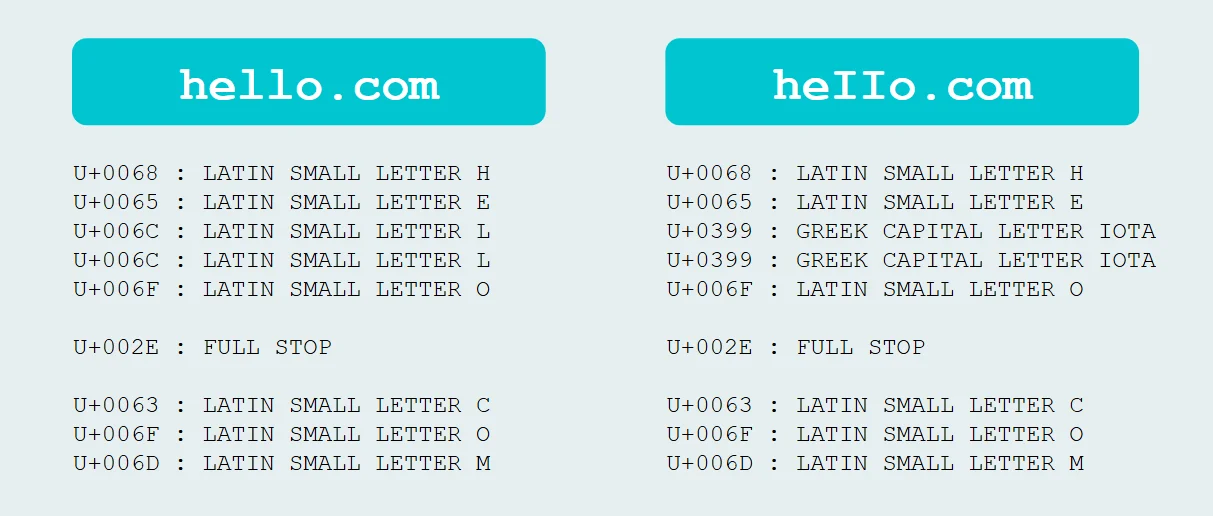
Potentially, yes. Some websites use other methods like "fingerprinting," which gathers unique information about your browser and device (like screen resolution, fonts, and plugins) to create a unique identifier. This method is harder to block than cookies.
Blocking all cookies can enhance privacy, but it may "break" some websites. You might be unable to log in, save preferences, or use shopping carts. A good middle ground is to block only third-party cookies.
Cookies can store information you provide, like your name or email, if you've entered it into a form on a website. They don't inherently collect it, but they can store what you volunteer. This is why it's important to be cautious on unfamiliar sites.
Yes. While rare, attackers can use malicious cookies or hijack existing ones to gain unauthorized access to your accounts or steal personal information. This is why secure connections (HTTPS) and up-to-date security software are crucial.




Related Resources


Protect What Matters
Secure endpoints, email, and employees with the power of our 24/7 SOC. Try Huntress for free and deploy in minutes to start fighting threats.