If you’re a regular visitor to our blog, you may remember a most fascinating voyage last year. We took a plunge to the darkest corner of the internet known as the dark web.
We were met with a horrifying realization: there seems to be a “dark web counterpart” for all of us. Marketers? Check. Sales reps? Check. Customer service? Check. Many of these sites on the dark web even mirror legitimate websites, featuring about us pages, product pages—even reviews!
You know shady shenanigans are our thing here at Huntress, so we decided to suit up and make our descent back to the dark web to see what’s happening these days.
Some Things Never Change
We couldn’t help but notice some similarities between what we found last year and what’s going on now.
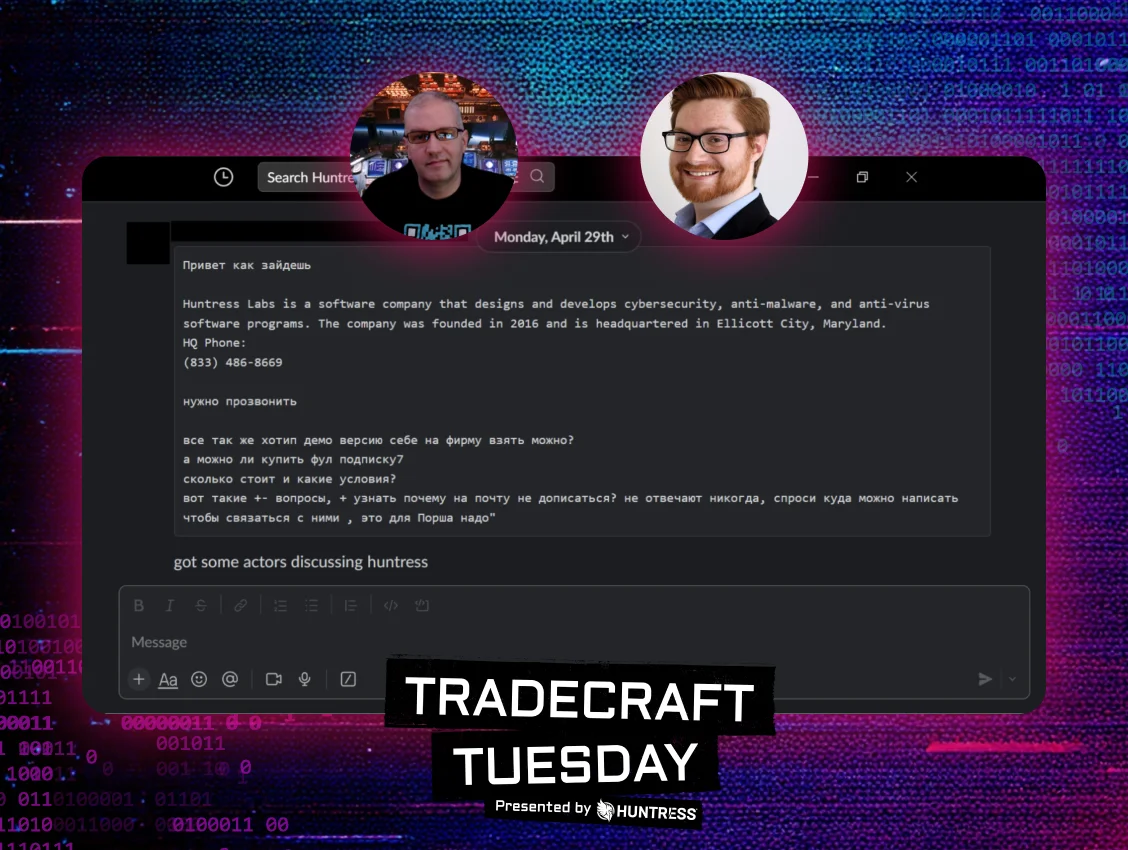
Much like we saw last year, bad actors are still sharpening their marketing and sales skills, diving head-first into promises of quality hacker tools, satisfaction guarantees and changed lives.
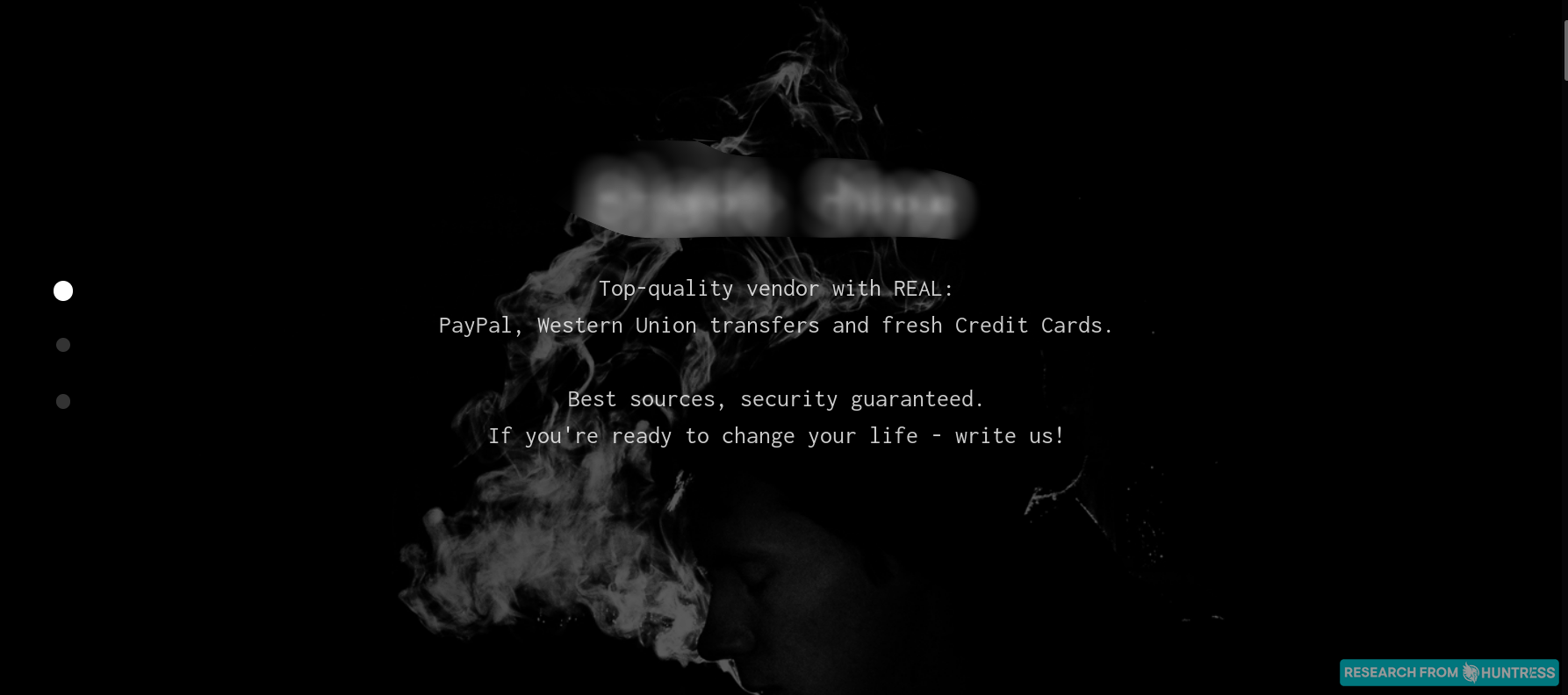

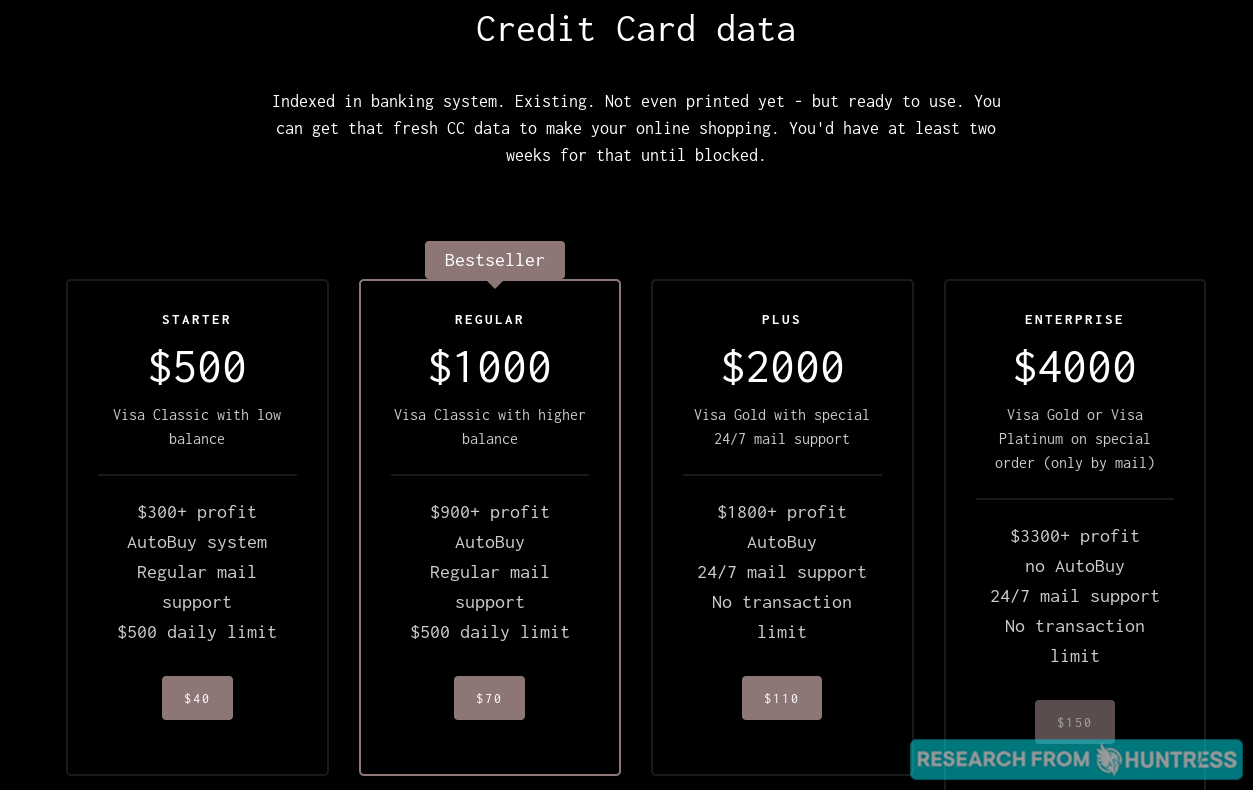
And what would a good deal be without a choice between tiers of services?
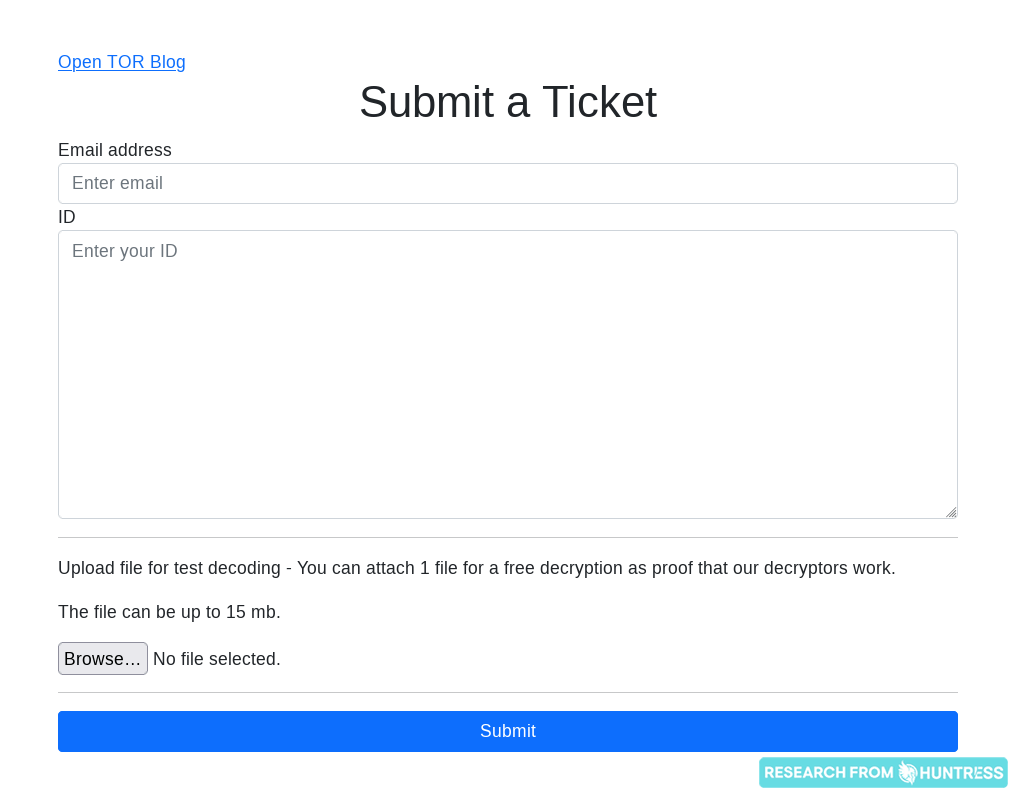
And this one was a bit interesting: one ransomware group clearly cares about customer satisfaction, as they dedicate an entire ticketing system to allowing prospects to chat with a real ransomware operator. Every good business relationship starts with positive interactions between people, right?
We also saw a number of dedicated FAQs across sites on the dark web last year. We stumbled across a particularly interesting list of FAQs during our latest dive to the dark web—this time on a site that sells compromised PayPal accounts.
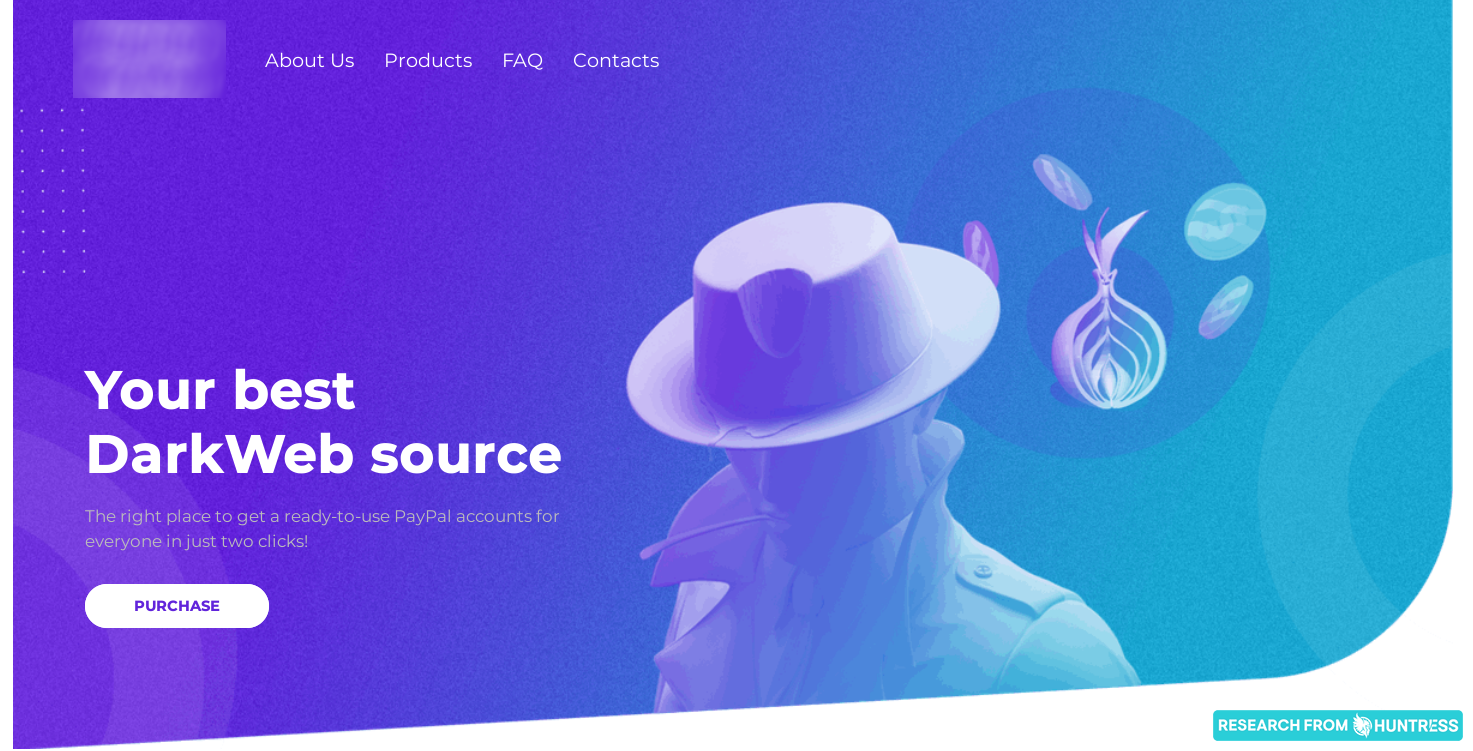

We also saw a number of dedicated FAQs across sites on the dark web last year. We stumbled across a particularly interesting list of FAQs during our latest dive to the dark web—this time on a site that sells compromised PayPal accounts.
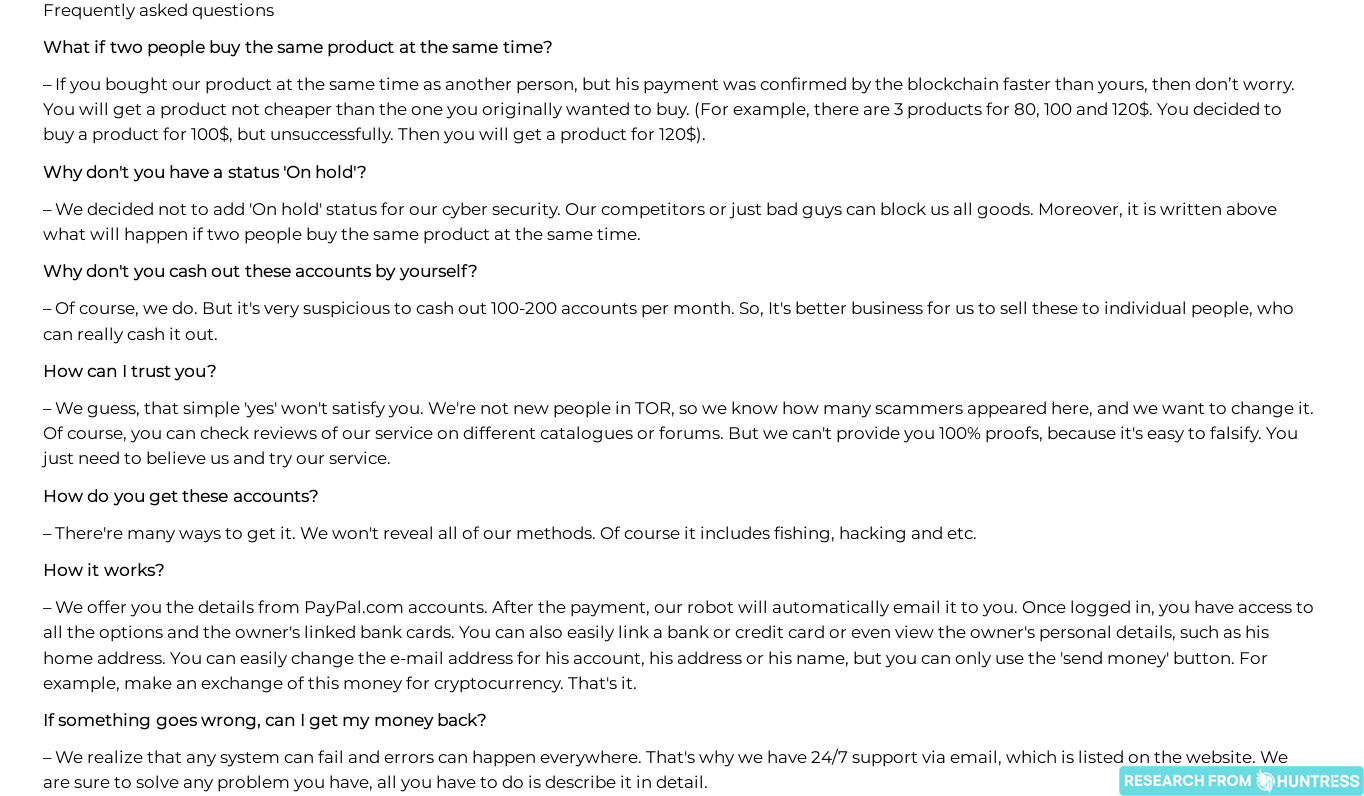
What’s really fascinating is these underground, organized cybercrime groups and their similarities to legitimate businesses. They explain their business models. They prove their “legitimacy” (as well as they can while maintaining anonymity). Many even offer money-back guarantees and 24/7 support. They even offer up testimonials from happy customers.
These are standards that legitimate businesses strive toward every day. When we say it’s likely you have a dark web counterpart, we really mean it. 😅
P.S. We’re still thinking about you, Rodrigo. 💙
Good News: The Hackers Still Have Ethics!
I think my favorite realization last year was that the same hackers who exploit businesses apparently have ethics. 👀
There’s an entire underground ecosystem for hackers who feel they’ve been wronged. It consists of plaintiffs, defendants and courtrooms—much like our legal system does.
What’s different is that the courtroom is actually an online forum:
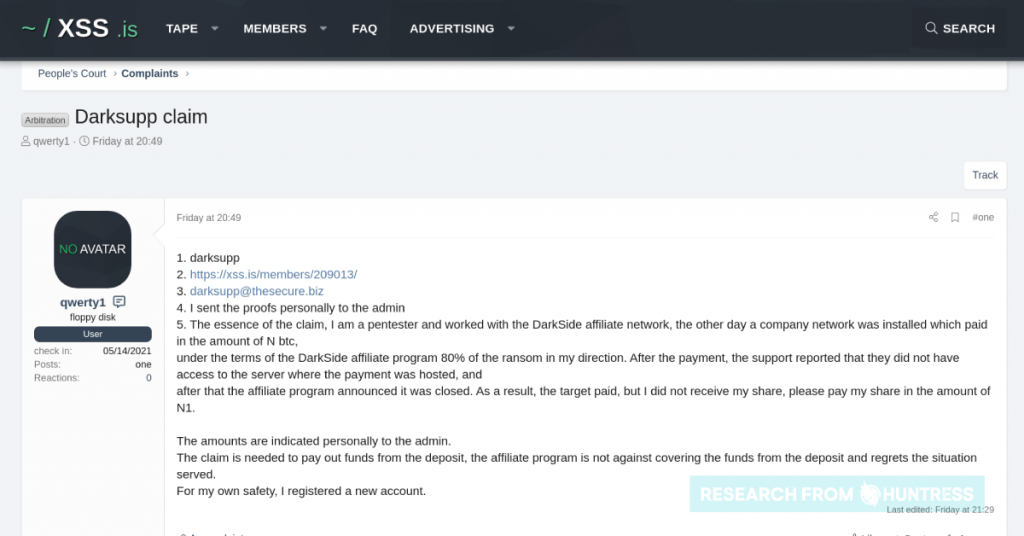
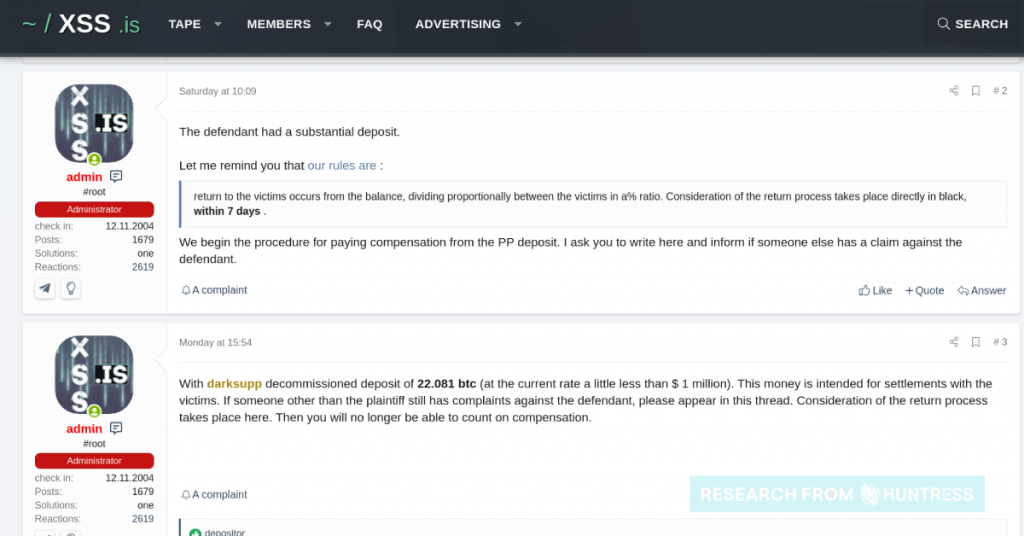
I’m overjoyed to say that the hackers are still taking pride in their ethics this year. 🥲
Take the below ransomware group, for example. They position themselves as real heroes, bringing awareness to the network security industry by working to “force business [sic] to develop IT defense and security.” They “inform the society about attacks and consequenses [sic], about information leaked to the hackers.”
On another page on their site, they list out a number of companies—from healthcare providers and government agencies to law firms—and gigabytes of those companies’ data, and each of these companies have been viewed tens of thousands of times.
(Image heavily redacted for obvious reasons.)
Guess it’s true: Not all heroes wear capes. 🥴
Another interesting tidbit we found: much like last year, dark web enthusiasts are still cognizant of all the scams that exist underground. Not scams of leaked data or hacking techniques, of course—scams such as hackers being ripped off by other hackers.
For starters, check out this strongly worded intro to one Tor “Scam List,” written by someone who’s clearly been burned in the past:
(It’s the “Honor and God are more important to me” that really gets me.)
The list goes on and on for all the “scams” identified—here’s one short snippet:
Stay safe out there, hackers. 🙃
But Then, a Wild University Appears
When John Hammond comes to you and says he’s just discovered what may be his favorite thing ever on the dark web, you know you’re in for a good time.
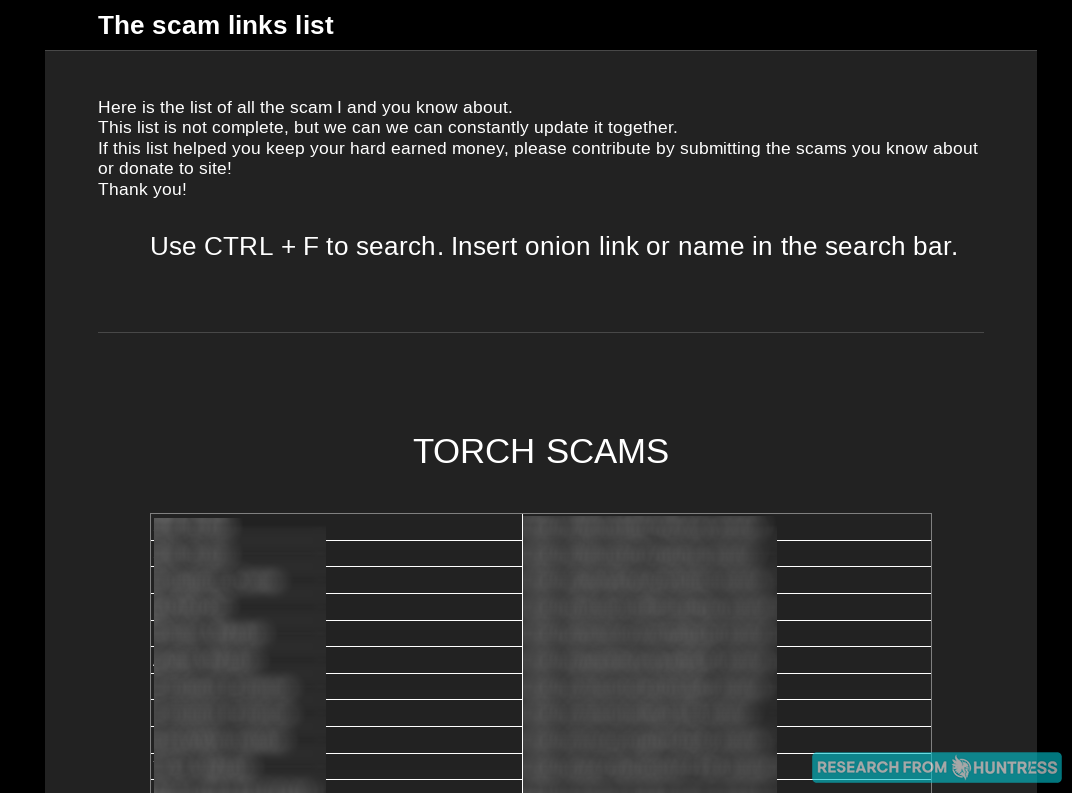
Just when we thought we’d seen it all, we find a cybercriminal university, and it’s exactly what it sounds like: a bonafide school for cybercriminals-in-training! What’s this world coming to?!
Folks, welcome to HackTown.
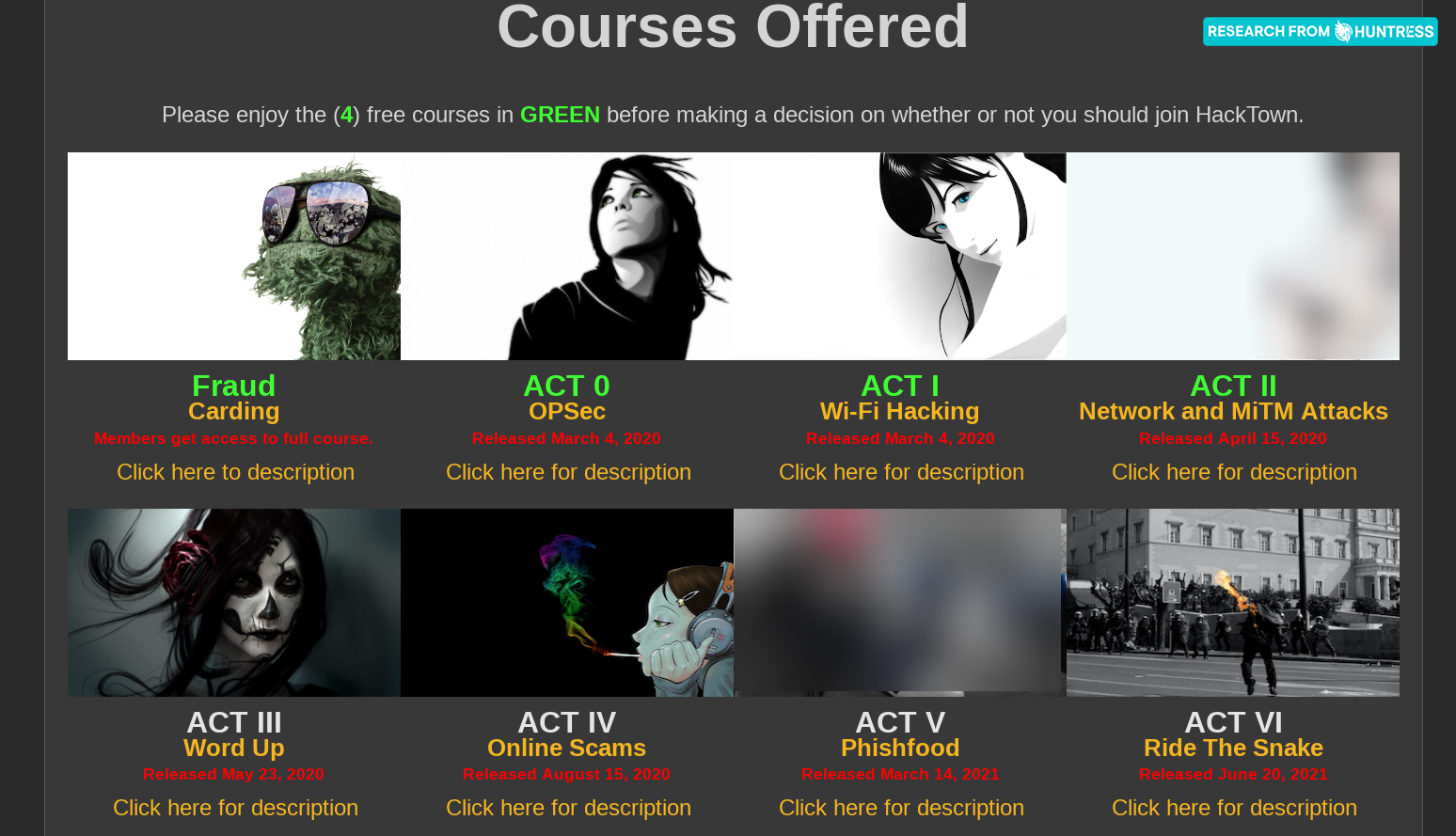
They offer a Cybercriminal Degree—or, for those not yet ready to make the full plunge, they offer a Carding Diploma for all your credit card fraud needs.
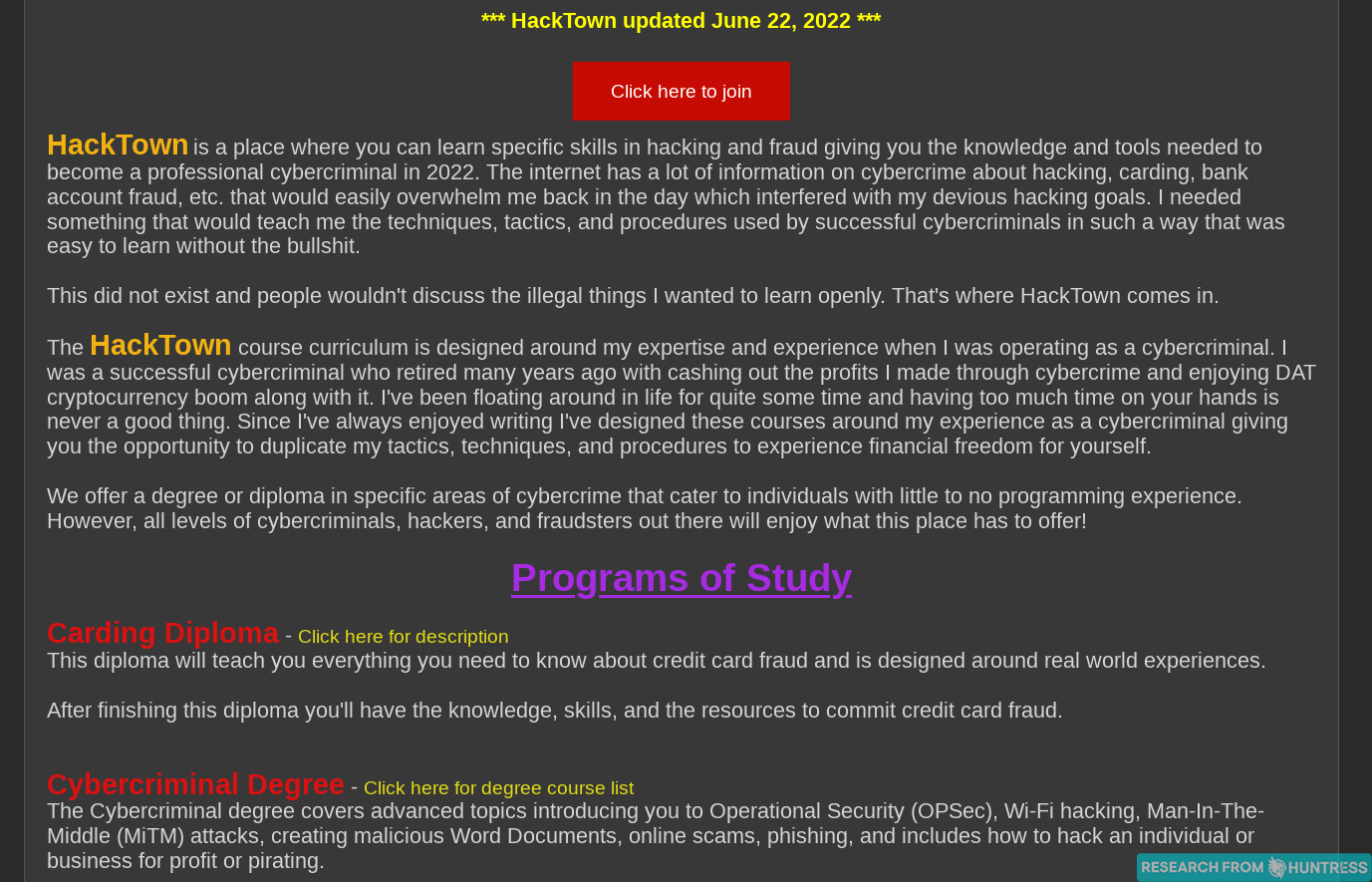
Not sure if you’re ready to whip out your credit card just yet? No worries—sample some free content!
When asked why there’s a membership fee at all, our hacking instructor has an answer:
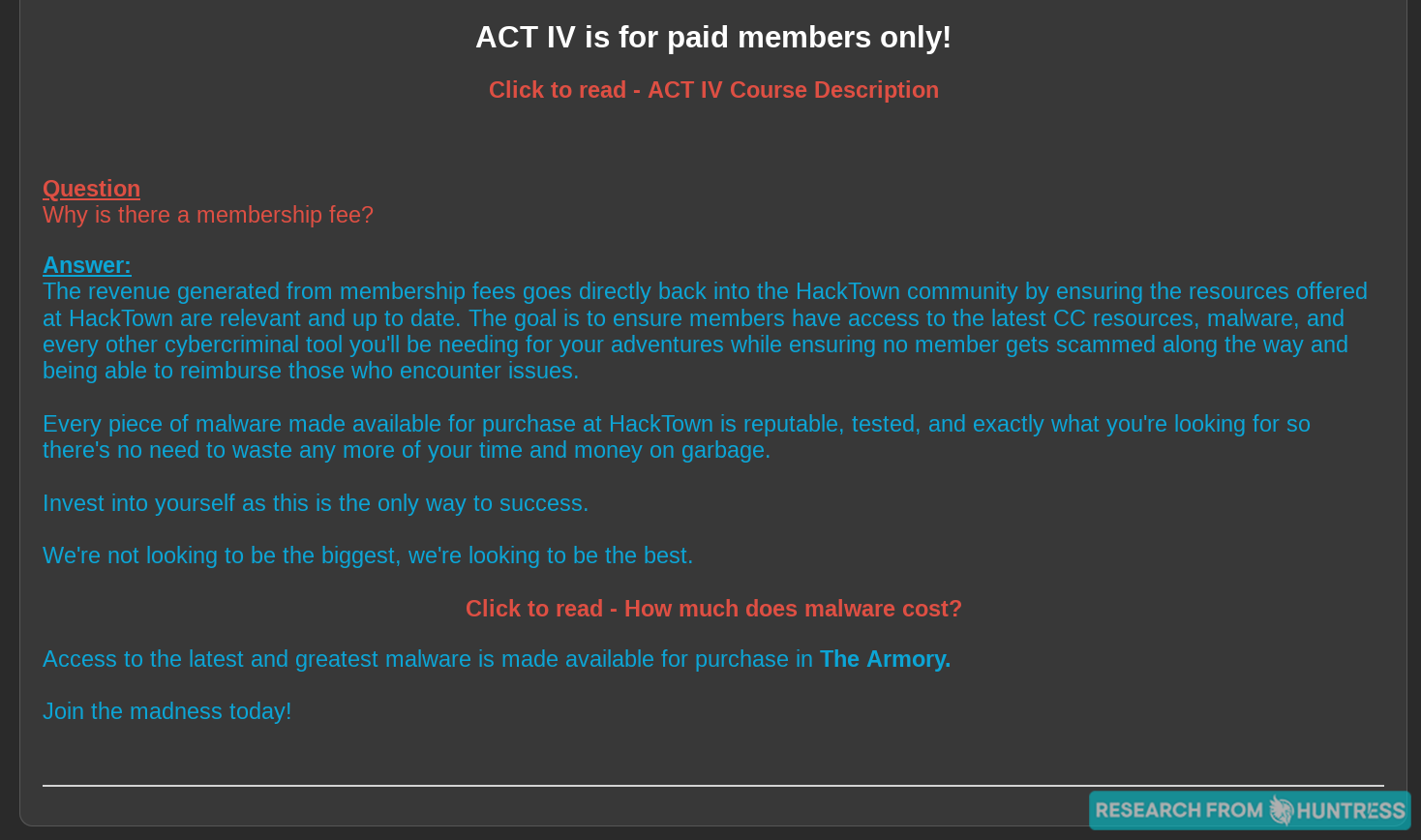
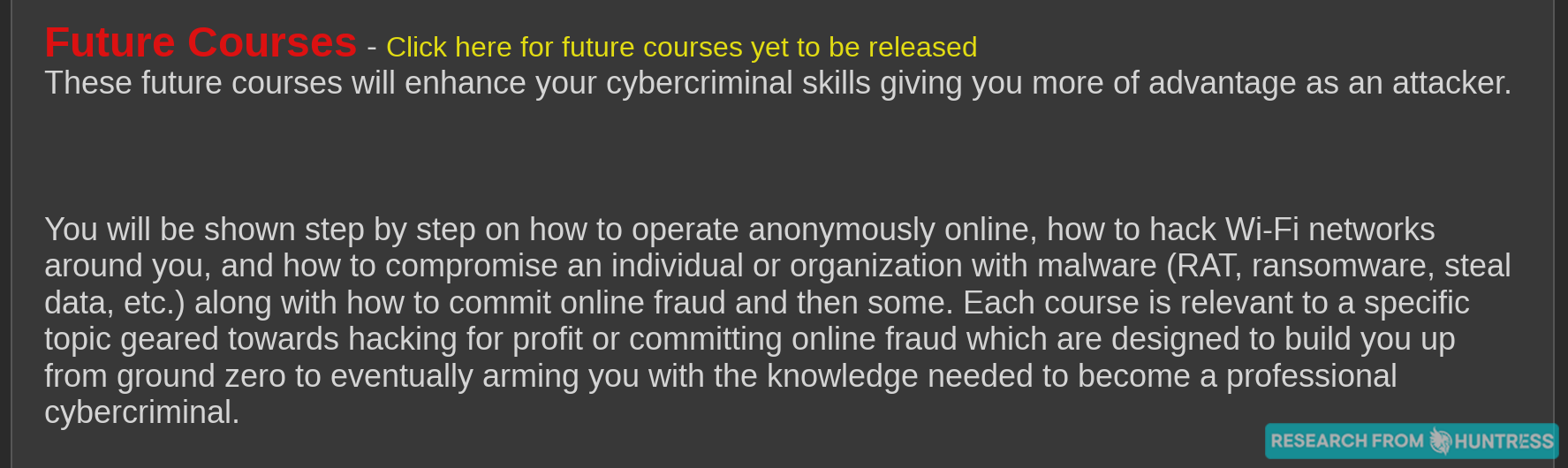
We just had to dig in a little deeper on their “Programs of Study.” We were not disappointed. Check out some of the course descriptions we uncovered.
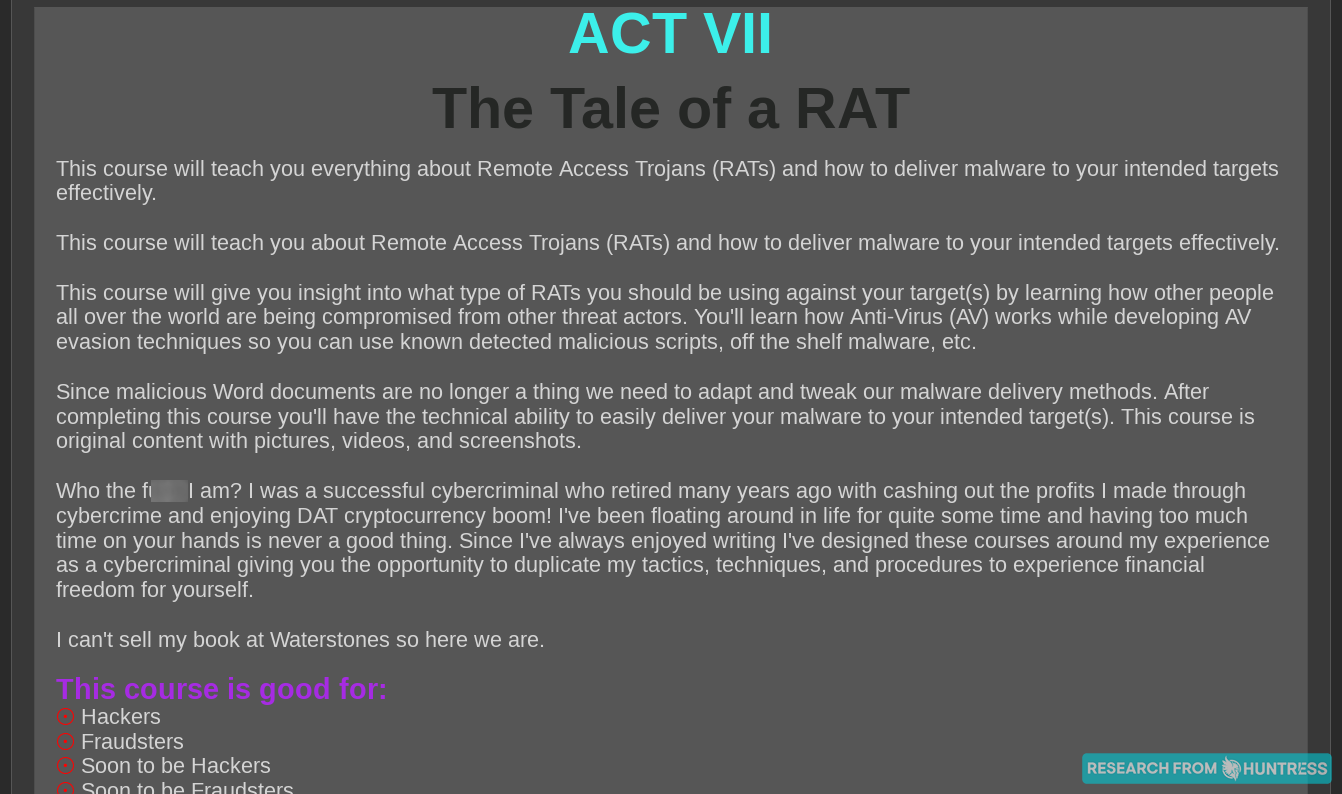
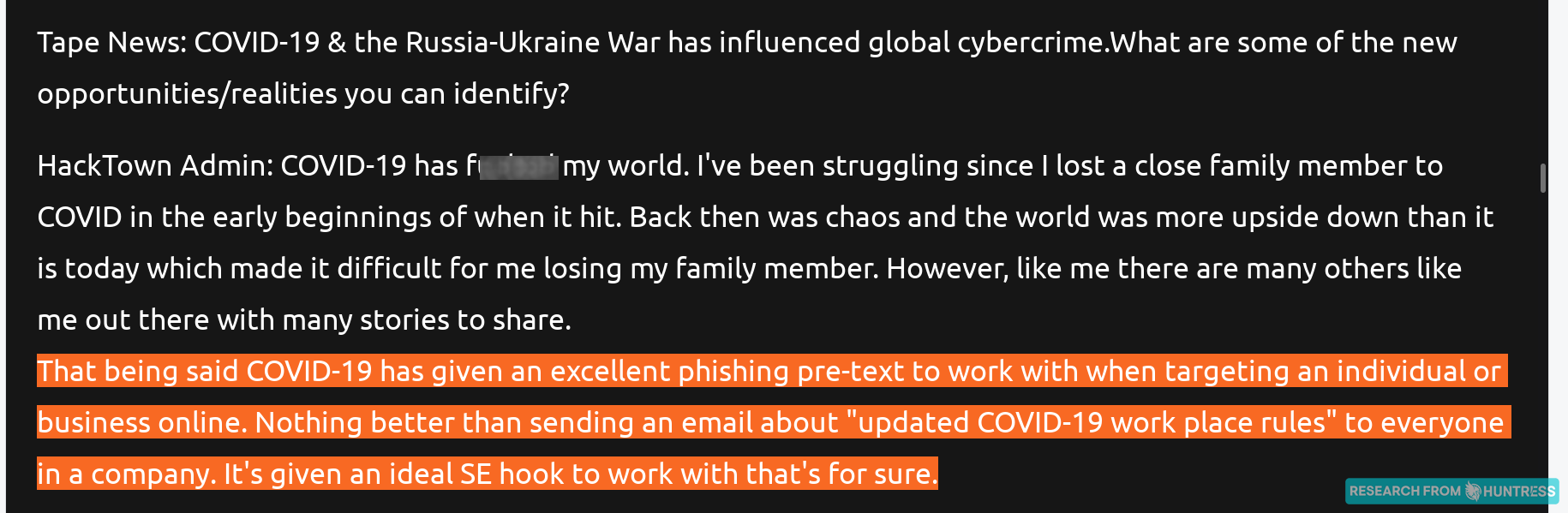
We learn a little bit about the “successful cybercriminal” behind these courses but wanted to learn more. Never fear: the mastermind participated in an interview to talk about their university.

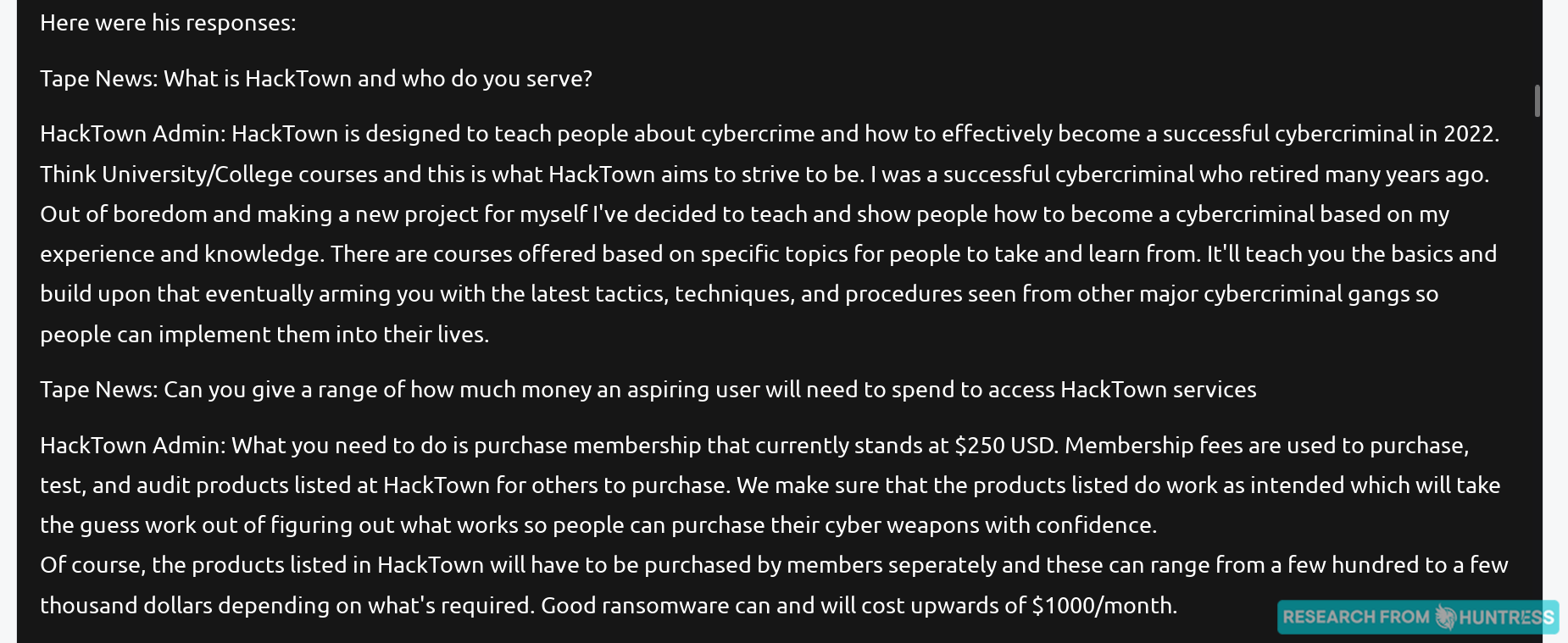
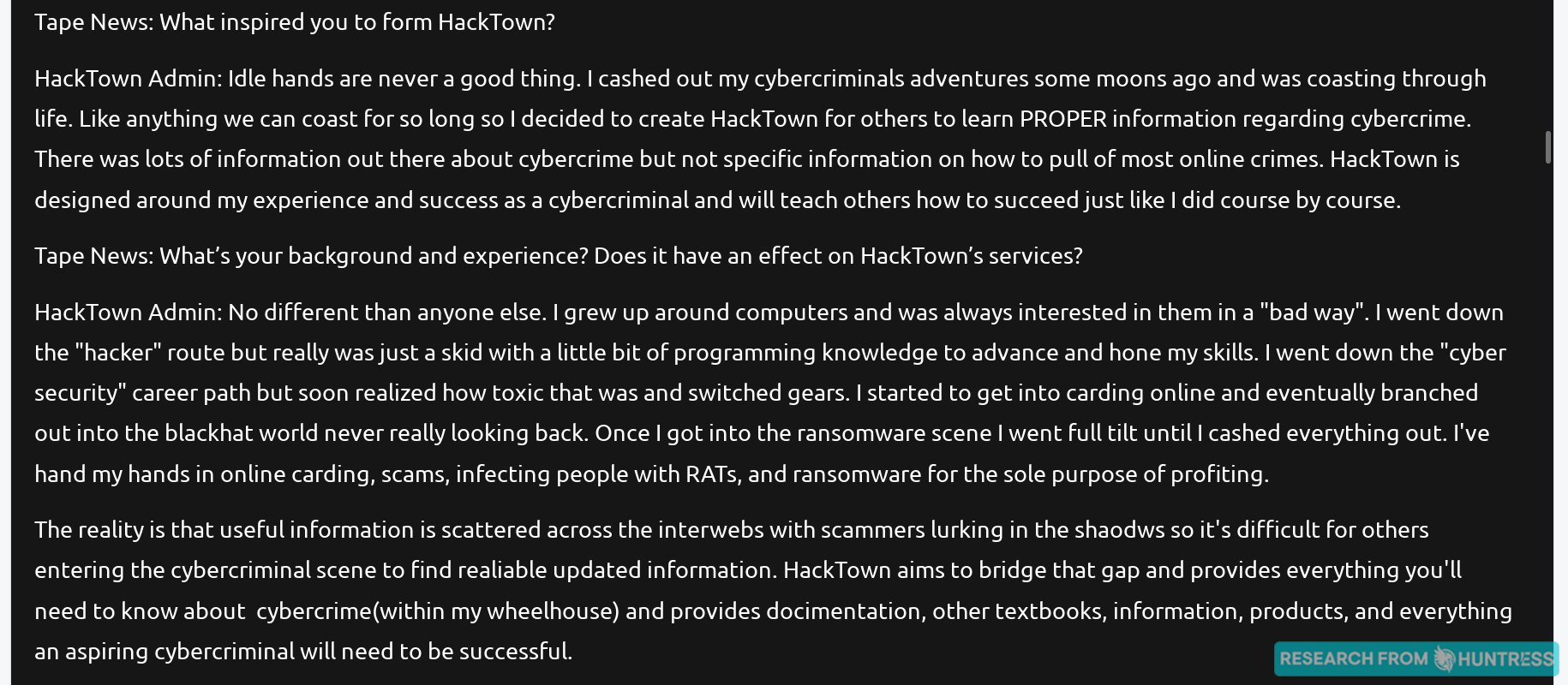
Defenders, take note:
And what would a dark web e-commerce experience be without reviews?!
For me, the realization I had last year that there are sites and businesses on the dark web that mimic legitimate businesses was a game-changer. This year, I’m with John—the idea of a university for cybercriminals is what stopped me in my tracks.
Just as we’re getting cybersecurity certifications and training under our belts, so are our adversaries. What a time to be alive.
***
I hope this year’s voyage to the dark web has been entertaining—and perhaps eye-opening. There really is a dark web counterpart for everyone (and apparently everything, including college!).
This is the reality of what we as defenders are up against. Anyone can be a hacker if they’re willing to pay for ready-to-use tools found on the dark web—or decide to pursue a cybercriminal degree to learn the tricks of the trade themselves. Opportunities abound for today’s hackers, forcing us defenders to think outside the box to figure out how we can outsmart hackers at their own game.
Stay vigilant out there. 👀
***
* Special thanks to our Senior Security Researcher John Hammond for his help with writing this blog.