
We sat down with Brian Harrell, VP of Security at AlertEnterprise, and talked about the NERC CIP-014 Standard. If you aren’t familiar with CIP-014 or just want to learn more, Brian gives some great advice on the standard and its purpose to increase physical security protections of utilities across North America. As a physical security expert, Brian was on the CIP-014 drafting team and gives some valuable insight behind the creation of the standard. Brian also discusses some options to consider even if CIP-014 doesn’t apply to your entity and some best practices to protect your facilities.
What is the purpose of CIP-014 standard and why is it important?
The NERC CIP-014 standard is the regulatory result of a significant physical security attack that happened a few years ago. A major transmission substation in Central California was attacked on April 16, 2013. Shooting for over 19 minutes, the attacker(s) destroyed, damaged, or degraded 17 electrical transformers that funnel power to Silicon Valley, resulting in over $15 million worth of damages. Prior to shots being fired, the attacker(s) first entered six AT&T fiber-optic telecommunications vaults, severing 911 and communication lines. The criminal(s) then proceeded to shoot over 100 7.62 mm rounds into transformers and other grid components. If the gunfire wasn’t already enough to destroy the transformers, they subsequently began to leak tens of thousands of gallons of transformer oil, causing them to overheat and shut down. In my opinion, there is no doubt that this was a sophisticated yet low-tech attack by attacker(s) with industry knowledge. Unfortunately, the attacker(s) have not been brought to justice and nobody to-date is sitting behind bars.
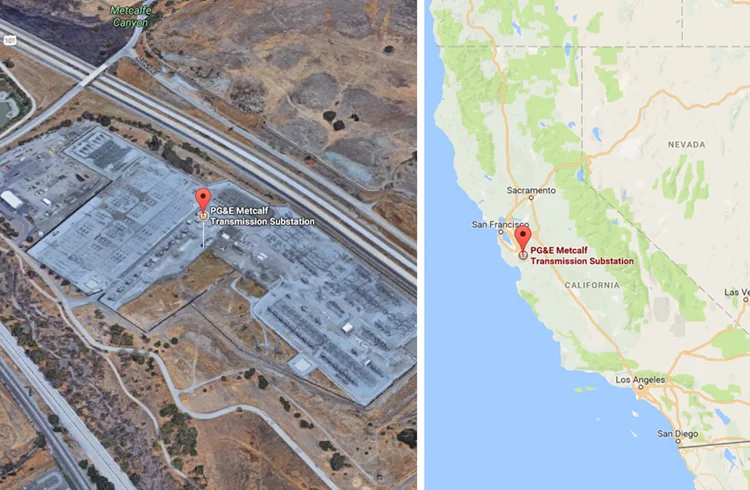
As a result of the Metcalf attack I just spoke of, the Federal Energy Regulatory Commission (FERC) ordered NERC, within 90 days, to develop a physical security standard designed to enhance physical security measures for the most critical Bulk-Power System (BPS) facilities, thereby lessening the vulnerability to physical attacks. As you can imagine, creating a standard and having industry, the NERC Board of Trustees, and FERC quickly approve it was a tall task.
Can you break down what is required under CIP-014?
Having been on the NERC CIP-014 Standard Drafting Team (SDT), we wanted to create a standard that targeted the most critical substations and control centers in North America – not the entire list of 55,000 transmission substations (> 100 kV) currently on the map. The goal was to harden infrastructure, manage risk, and be mindful of the time in which it would take to add improvements along with the cost. The conversations centered on particular substations that if rendered inoperable or damaged as a result of a physical attack could result in instability, uncontrolled separation, or cascading within an Interconnection.
There are six requirements within CIP-014 that Registered Entities must comply with, if you meet the inclusion criteria. The inclusion criteria can be a bit complicated, but at a high level, if you have a 500 kV substation, or a 200-499 kV substation that is connected to three or more other substations (200 kV or higher), you are likely subject to the standard. Additional criteria are listed, so take a look.
Here is the requirement breakdown:
R1. Perform an initial transmission risk assessment. This analysis is designed to identify substation(s) that if rendered inoperable or damaged could result in instability, uncontrolled separation, or cascading within an Interconnection. This needs to happen once every 30 calendar months.
R2. The Transmission Owner needs to have an unaffiliated third-party verify the initial risk assessment to determine if the substation is critical.
R3. If an entity (Transmission Owner) has a primary control center that can operationally control the substation, they would need to notify the Transmission Operator (TOP).
R4. If you identified a substation, or a primary control center in R1, verified according to R2, and made notifications according to R3, you will need to conduct a security threat and vulnerability assessment (TVA) against those substations(s) and primary control center(s). This assessment should consider prior security events such as vandalism and sabotage, as well as threat warnings from law enforcement, the Electricity Information Sharing and Analysis Center (E-ISAC), and other U.S. or Canadian governmental agencies.
R5. Based off the threats and vulnerabilities discovered in R4, the Entity would now need to develop a physical security plan designed to deter, detect, delay, assess, communicate, and respond to these potential physical threats and vulnerabilities.
R6. Once the TVA has been conducted, and a physical security plan has been put in place, the Entity must have an unaffiliated third-party review R4 and R5. The reason we added this requirement is that we felt it was important to inject qualified experts into the compliance process as it adds a deeper understanding of physical security and a fresh set of eyes.
How many utilities does CIP-014 affect in North America and should they be worried?
I can recall sitting around the table, early on during SDT meetings, where numbers were discussed and we always prefaced the “numbers” conversation in the context of reducing risk to the most critical substations. That was the ultimate goal, and I think we succeeded. That said, the early projections were that the standard was likely to capture approximately 500 substations and primary control centers. Now that the compliance process has played out, my estimation is that this number is closer to about 1,500 CIP-014 sites. NERC and the Regions have done a very good job with outreach and communicating compliance guidelines. I don’t think utilities should be worried, but if they have concerns, they should contact their regulator or a trusted consultant for guidance.
"Now that the compliance process has played out, my estimation is that this number is closer to about 1,500 CIP-014 sites."
What are some of the typical challenges implementing a CIP-014 program?
A few challenges exist. First, many utilities feel that in order to come into compliance they must spend millions of dollars overnight. As a matter of fact, NERC and the Regions have been very flexible with the implementation of additional security measures. The regulator fully understands that it takes time to plan and allocate the capital funding, and then hire contractors and consultants to install fencing, cameras, access control, etc. So, when building your physical security plan (R5), use what I call “future state” language. Meaning, you can articulate that you are going to update, install, and add security protective measures in the future, but be clear on completion dates. You must also be reasonable in your timing – not more than 2 ½ years from the time in which you write the security plan (R5).
"Use what I call “future state” language. Meaning, you can articulate that you are going to update, install, and add security protective measures in the future, but be clear on completion dates."
Next, CIP-014 was never meant to be a “check the box” compliance standard with a cookie cutter approach. Every TVA (R4) and physical security plan (R5) is unique to that substation or primary control center. It’s imperative that for every plan that is written, it is specific to that site. This requires engaging local law enforcement and truly understanding the threats placed on that facility. What are the geographical threats, line-of-site issues, and frequency of vandalism and/or sabotage? Additionally, how are you detecting threats and maintaining situational awareness on what is considered a critical substation to the power grid? The days are gone where industry has a high-voltage substation out in the middle of nowhere, unmanned, and not monitored.
Even if CIP-014 doesn’t apply to my entity, what could I be doing to protect my assets?

Great question! Most substations will not fall under CIP-014, but that doesn’t mean they aren’t critical to a utilities’ business or reputation. Every utility should consider the following items when thinking about securing a “critical” site or creating a security plan.
- Perimeter Security
- Access Control
- Lighting
- CCTV/Cameras and Remote Monitoring
- Intrusion Detection
- Entry/Exit hardening
- Line-of-sight Gunfire Mitigation
- Standoff Distances to Critical Assets
- Key and Lock Program
- Visitor Access
- Security Signage
- Personnel Screening and Background Checks
- Insider Threat
- Drones and the Overhead Threat
- Use of Security Patrols
Any other advice or resources when it comes to learning more about implementing a CIP-014 program?
A great resource for utility security is the American Public Power Association (APPA) Physical Security Essentials Primer that came out last year. If you are looking for guidance, checklists, and industry best practices, you will certainly find this useful.
It can be assumed that at some point, a North American utility will again suffer from a planned and coordinated attack against its electric infrastructure. Have these utilities examined credible threats closely enough? Did they prepare to respond, recover, and communicate? As an industry, many will be judged and hard questions will be asked about how seriously threats were considered and what was done to mitigate future attacks. Success will be determined by how quickly the industry responds and the swiftness of system recovery.








