It’s not exactly breaking news that cyber threats to critical infrastructure have become a major concern for state and local governments. But if it feels like the climate has gotten even worse recently, you’re not alone—the federal government agrees.
Back in January 2024, FBI Director Christopher Wray testified before Congress and explained how hackers from the Chinese government are actively trying “to find and prepare to destroy or degrade the civilian critical infrastructure that keeps us safe and prosperous.” According to Wray, the hackers are continually “positioning on American infrastructure in preparation to wreak havoc and cause real-world harm to American citizens and communities, if or when China decides the time has come to strike.”
If Wray's testimony seems a little frightening, it should be. Let's take a closer look into the current cyber threat landscape and discuss how public entities can fulfill their obligations of safeguarding their communities from potential attacks.

The Current Cyber Threat Landscape
Cyberattacks targeting critical infrastructure have escalated in recent years, posing huge risks to national security and public safety. From attempts to disrupt energy grids to breaches aimed at compromising transportation networks, these attacks have shown clear vulnerabilities in many of our essential systems. Even small-scale attacks can have far-reaching consequences.
Notable Infrastructure Attacks Over the Last 15 Years
- Back in 2009, hackers from China and Russia snuck into America's power grid network, planting malware that could be activated in the future. Then, in 2010, Russia took a swing at NASDAQ, and not just for data— they also left behind a virtual “bomb” that could be “detonated” in the future, potentially crippling financial networks.
- In 2013, Iranian hackers almost flooded a New York town by tampering with the Bowman Avenue Dam's control systems.
- In 2017, Russian hackers targeted the Wolf Creek nuclear plant in Kansas, and in 2022, they hit a food company, causing a meatpacking plant shutdown across the US.
- China breached New York City's subway system in 2021, and just recently, Microsoft sounded the alarm about the China-backed Volt Typhoon gang infiltrating the critical infrastructure of Guam—a US territory and home of two strategic US military bases.
- In 2021, a ransomware attack paralyzed the Colonial Pipeline, leading to fuel shortages and economic disruptions. Similarly, the devastating SolarWinds supply chain attack one year prior exposed vulnerabilities in both government and corporate networks, highlighting the far-reaching impact of modern cybersecurity threats to critical infrastructure.
These threats are not going away. In its most recent Annual Threat Assessment, the Office of the Director of National Intelligence echoed Wray’s concerns, stating that “China almost certainly is capable of launching cyberattacks that could disrupt critical infrastructure services within the United States, including against oil and gas pipelines, and rail systems.”
What Happens Next?
As you can imagine, the consequences of future cyberattacks on critical infrastructure could be catastrophic. Disruptions to essential services such as energy, transportation, and healthcare could lead to widespread chaos and economic losses (the average cost of a ransomware attack in 2022 was more than $4.5 million, according to IBM).
Plus, the fact that many of the most important infrastructure systems are interconnected could further amplify the impact of attacks and create a “polycrisis.” In other words, one single attack on a smaller system or network could cause a domino effect that cripples several others connected to it.
Stay Resilient Against Cyber Threats to Critical Infrastructure
The truth is that public entities now play arguably the biggest role in defending against cyber threats to critical infrastructure. Today’s state and local governments must acknowledge this massive responsibility by prioritizing cybersecurity and allocating resources to bolster their defenses against these threats.
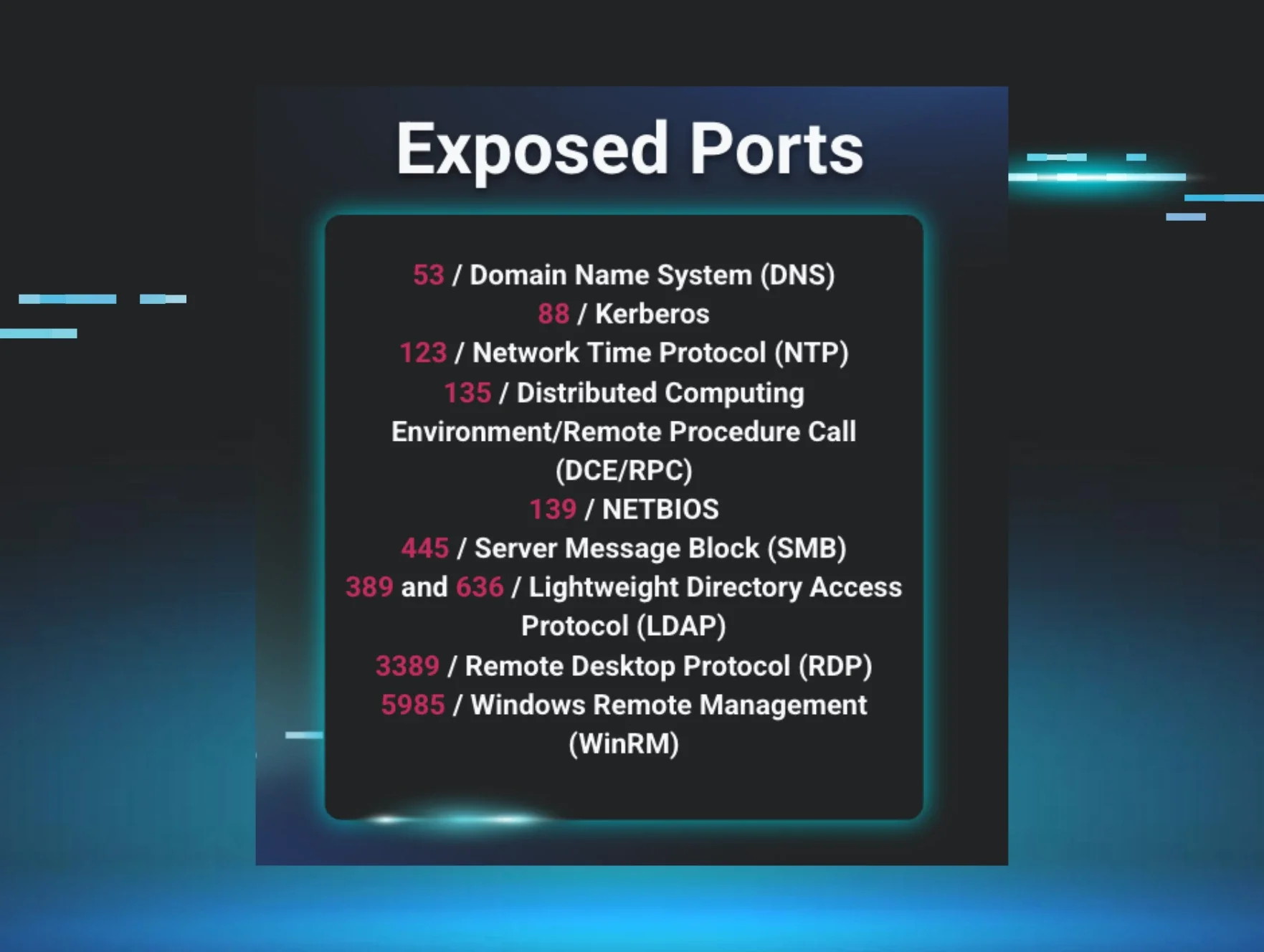
Let’s be clear here: investing in robust cybersecurity measures, conducting regular risk assessments, educating employees about cybersecurity, and fostering collaboration with federal agencies and private sector partners are all now considered essential steps to safeguard critical systems and networks—not merely best practices.
By leveraging advanced threat detection capabilities and proactive monitoring, Huntress helps organizations identify and neutralize potential threats before they escalate.
Find out how Huntress can help safeguard private data, protect critical infrastructure from malicious actors, and ensure the safety and well-being of your communities in the midst of constant threats. Request a free demo to see for yourself.